Brandon Bailey:
But the idea that Farook might have used the phone to transmit a “lying-dormant cyber pathogen” into county data systems is a new one. Ramos’ office, however, cited it in a court filing Thursday among several other reasons to support the government’s position.
“This was a county employee that murdered 14 people and injured 22,” Ramos said. “Did he use the county’s infrastructure? Did he hack into that infrastructure? I don’t know. In order for me to really put that issue to rest, there is one piece of evidence that would absolutely let us know that, and that would be the iPhone.”
The argument drew condemnation from one software expert who has signed a brief in support of Apple’s position.
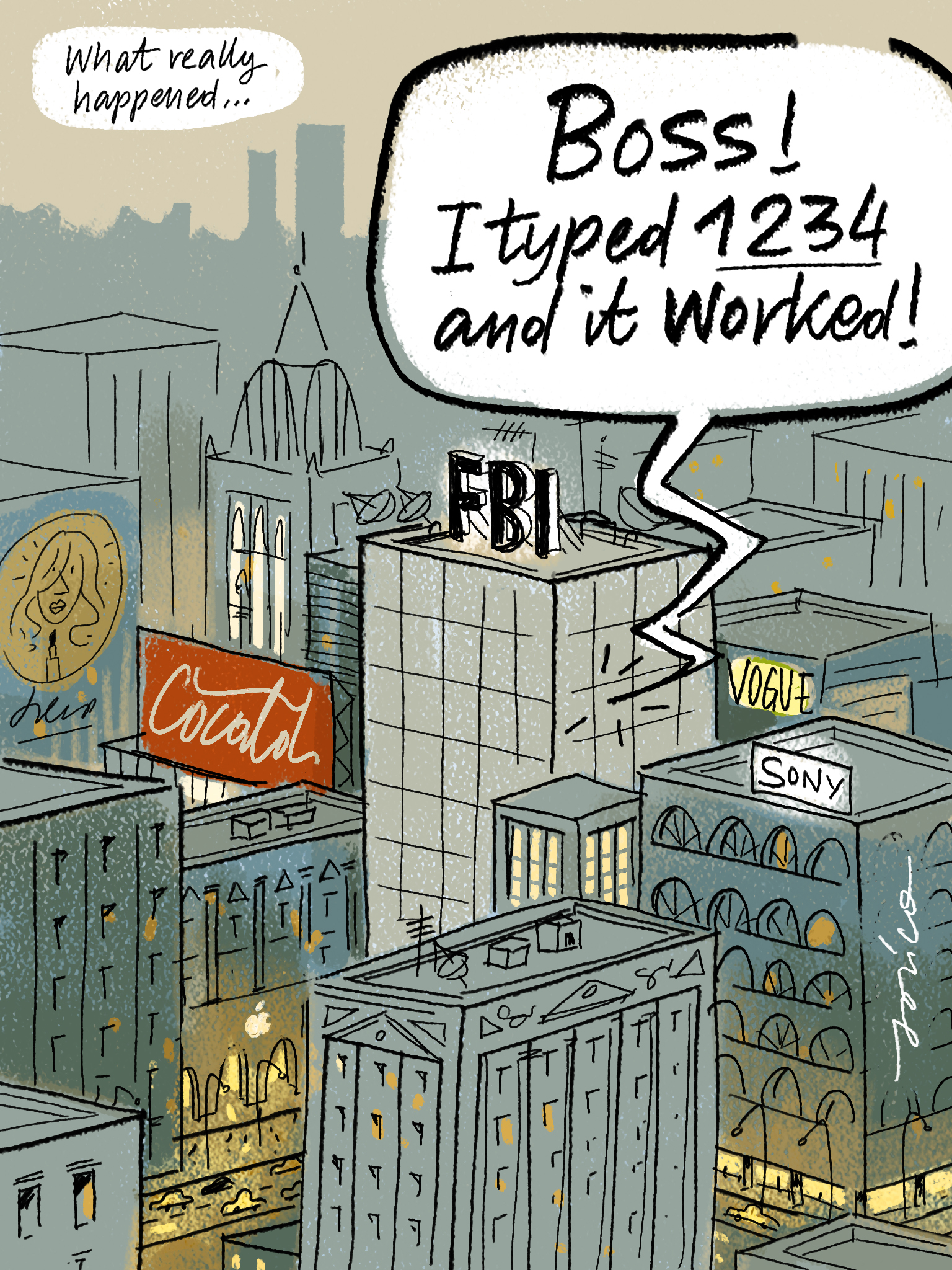
“Ramos’s statements are not only misleading to the court, but amount to blatant fear mongering,” independent software researcher Jonathan Zdziarski wrote in a post on his personal blog .
Other security experts who haven’t taken sides also discounted the scenario. “It’s definitely possible, technically, but it doesn’t seem to me at first glance to be likely,” said David Meltzer, a computer security expert and chief research officer at Tripwire, a commercial IT security firm. He said Apple’s iPhone operating system is a relatively closed environment that’s designed so users can’t easily introduce their own programs.
Ramos, meanwhile, said he’d heard about social media posts that mocked the term “cyber pathogen,” which is not generally used by tech experts. “When they do that,” he said, “they’re mocking the victims of this crime, of this horrible terrorist attack.”
Using the victims of a terrorist attack to further their own agenda however, that’s much worse.